HealthTech platforms operate as distributed SaaS ecosystems that manage patient records, power telehealth interactions, and connect multiple healthcare systems through APIs.
This level of complexity creates a new reality: scaling development teams is no longer just an operational decision. It directly affects how organizations protect Protected Health Information (PHI) and maintain compliance with frameworks such as HIPAA and SOC 2. When companies need to grow fast without compromising security, the question becomes unavoidable: Staff Augmentation or Outsourcing?
Why Staff Augmentation vs Outsourcing for HealthTech Is a Compliance Decision
In most industries, choosing a delivery model focuses primarily on cost and speed. In the HealthTech sector, the equation changes entirely. Here, compliance requirements make your team structure a fundamental part of your security model.
The Healthcare Regulatory Framework
To understand this, we must look at the two primary standards governing healthcare software:
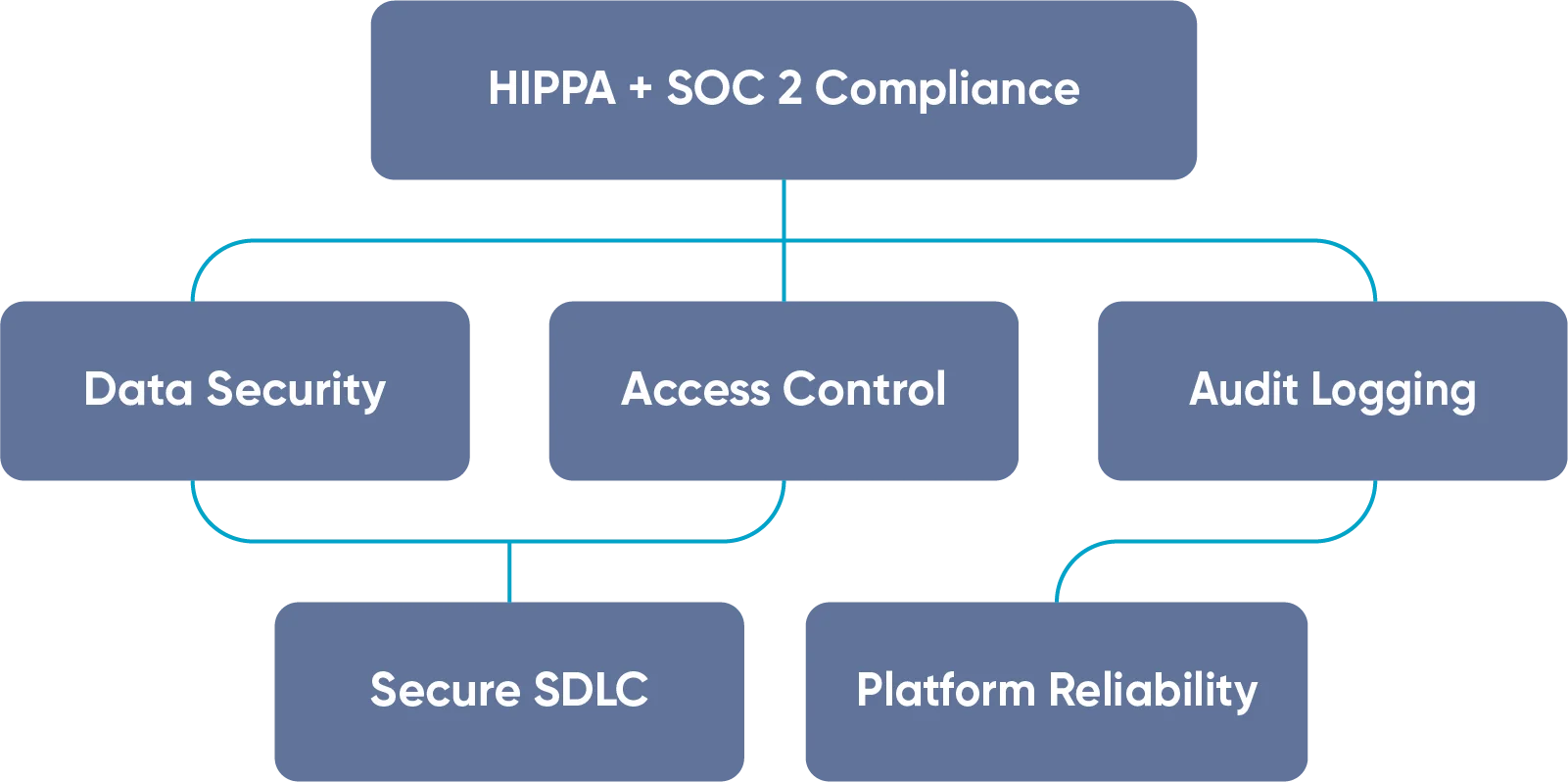
- HIPAA: Outlines the requirements organizations must follow to safeguard Protected Health Information (PHI). It requires strict access control, end-to-end encryption, and full auditability of all data interactions.
- SOC 2: Extends these requirements by focusing on overall system availability, security processes, and operational consistency.
Defining the "Compliance Boundary"
These frameworks do not stop at the infrastructure level; they apply directly to your development workflows. Every engineer with access to code repositories, staging environments, or databases becomes an official part of your compliance boundary.
If an engineer is part of an external outsourcing firm with their own separate security protocols, that boundary becomes fragmented and harder to audit.
The Foundation of Scalability
According to healthcare SaaS best practices, security must be integrated into architecture and development processes from the start. This means that the way you scale your team—whether by integrating augmented staff into your environment or handing off projects to an outside vendor—directly determines how effectively you can enforce and demonstrate compliance during an audit.
Defining the Models in a Regulated Context
1. The Outsourcing Model (Project-Based)
In a traditional outsourcing model, a company hires an external vendor to deliver a specific product or feature. The vendor manages the team, the process, and the timeline. While this removes the management burden from the client, it often creates a "visibility gap" regarding how data is handled during the development process.
2. The Staff Augmentation Model (Team Integration)
Staff augmentation involves adding specialized engineers directly into your existing team. These developers follow your internal workflows, use your security tools, and report to your managers. For HealthTech, this means they operate entirely within your HIPAA-compliant environment.
Full Risk Comparison for HealthTech: Staff Augmentation vs. Outsourcing
When analyzing staff augmentation vs outsourcing for healthtech, risk must be evaluated across multiple dimensions.
| Dimension | Staff Augmentation | Outsourcing |
| Operational Control | Full internal control | Shared or external control |
| Security Enforcement | Consistent across teams | Varies by vendor |
| Compliance Alignment | Directly enforced | Indirect and harder to validate |
| SDLC Visibility | Complete | Partial or limited |
| Audit Readiness | High transparency | Documentation gaps possible |
| Data Exposure | Controlled environment | Increased external exposure |
| Incident Response | Immediate and internal | Dependent on the vendor |
This comparison shows that risk does not come from outsourcing itself, but from reduced visibility and control.
Building a Healthcare Compliant Nearshore Ecosystem
The success of staff augmentation in HealthTech depends on the quality of the partnership. A reliable nearshore partner must demonstrate more than just technical expertise; they must demonstrate a mature security culture.
This includes how the company manages its physical and digital infrastructure. For organizations in the US and Canada, working with partners in Latin America offers the advantage of proximity and similar time zones, but security must remain the top priority.
Compliance is not a checkbox. It is a continuous process that requires total alignment between the organization and its extended team.
The "Visibility Gap" Risk in Outsourcing
For HealthTech platforms, the biggest risk of outsourcing is the lack of control over the development environment. If a vendor develops a feature on their own local servers and then pushes the code to you, a "shadow" environment is created.
Under HIPAA, every environment that touches PHI must be secure. If you cannot audit the vendor’s internal access logs or verify who had access to the database during testing, you face a significant compliance liability.
Why Staff Augmentation Wins for HIPAA Compliance
Staff augmentation eliminates the visibility gap by ensuring a Unified Compliance Framework.
- Direct Access Control: You manage the permissions. If an engineer leaves, you revoke access instantly.
- Consistent Tooling: Everyone uses the same encrypted communication channels and VPNs.
- Audit Readiness: Since the augmented staff works in your environment, your internal logs capture every action, making SOC 2 audits much simpler.
Vetting a Partner: Questions for HealthTech Leaders
When evaluating a nearshore partner, vetting their internal processes is non-negotiable. Ask these critical questions:
- Do you have experience with SOC 2 or ISO 27001? These indicate a mature security culture and verifiable standards.
- Can you support our audit requirements? The vendor must provide clear records of development activity and access logs.
Scale Your HealthTech Delivery with AssureSoft
In a regulated market, your team is your security perimeter. AssureSoft provides nearshore engineers who integrate directly into your compliance boundary, eliminating the "visibility gaps" of traditional outsourcing. Maintain your development velocity without compromising audit readiness.

